After installing XG firewall you will have a functioning system. There are however some initial steps I’d recommend to adjust for your basic setup. This post describes my advise on how to configure your new firewall for home use.
Of course you will first need to setup the XG Firewall, if you haven’t done so, then you can follow my article: Installing Sophos XG Firewall Home Edition.
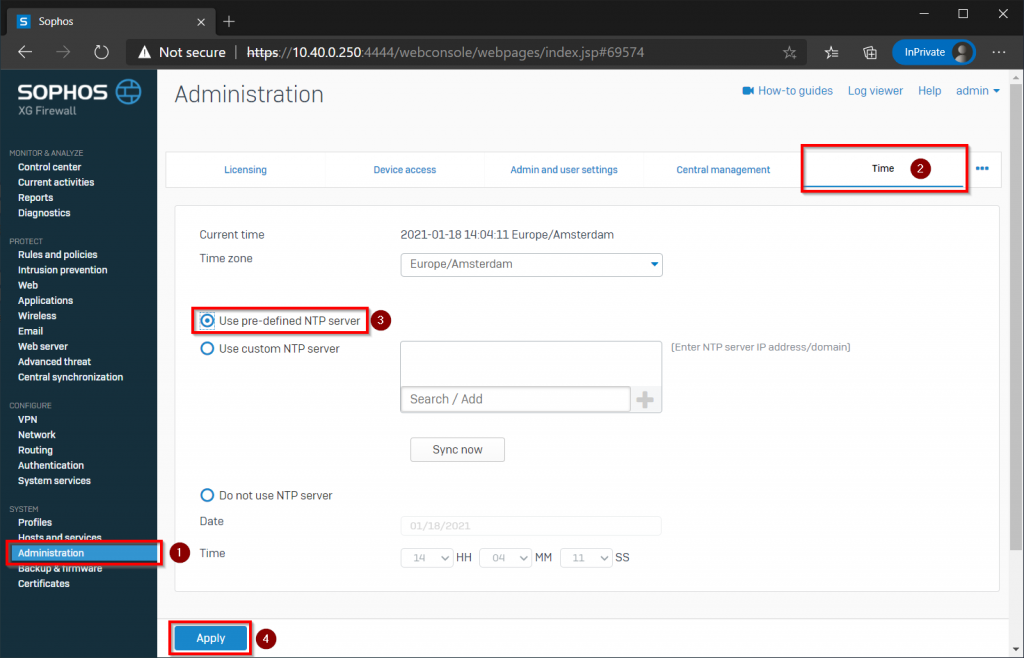
1 Setup automatic time synchronization
Your new firewall will log anything that happens on the network. If you want to trace back certain incidents, it is important that the time of the firewall is set correctly. To make sure the time is always correct, first go to System -> Administration and then the Time tab. Check the time zone (usually you will have already chosen the correct time zone during setup) and enable the option ‘Use pre-defined NTP server‘ before clicking on Apply.
2. Configure DoS and Spoof Protection for your home firewall
Under Protect -> Intrustion prevention go the the tab ‘DoS & spoof protection’. Scroll down and select ‘ARP hardening’.
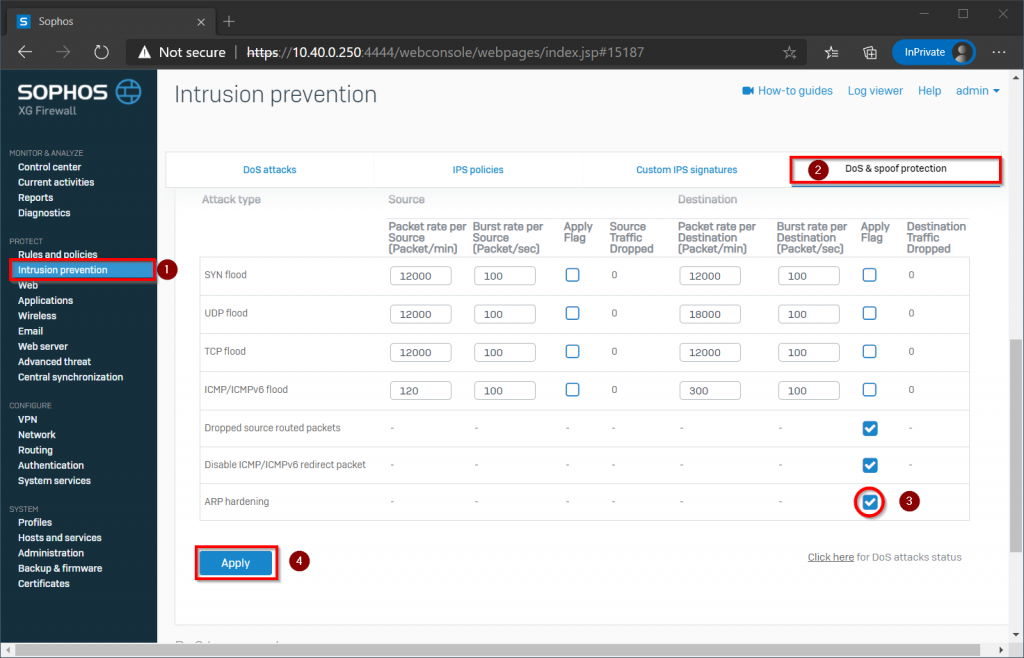
By enabling this option the firewall will never forward ARP-packets to other destinations nor accept them coming from the internet.
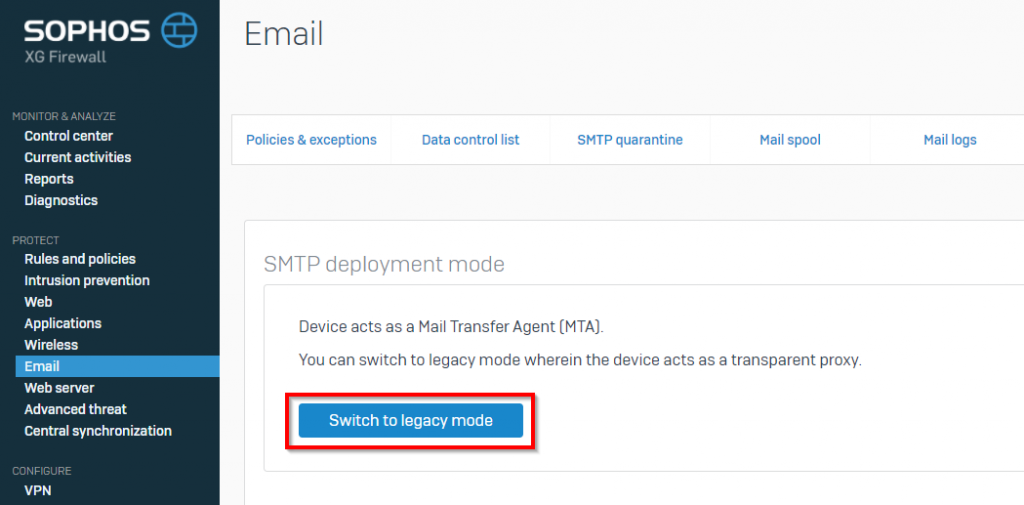
3. Configure Email for your home firewall
Under Protect -> Email choose the tab ‘General settings’ and click on the button ‘Switch to legacy mode’. I’m not sure why, but as long as MTA mode is active, in my own home environment I don’t get any email out.
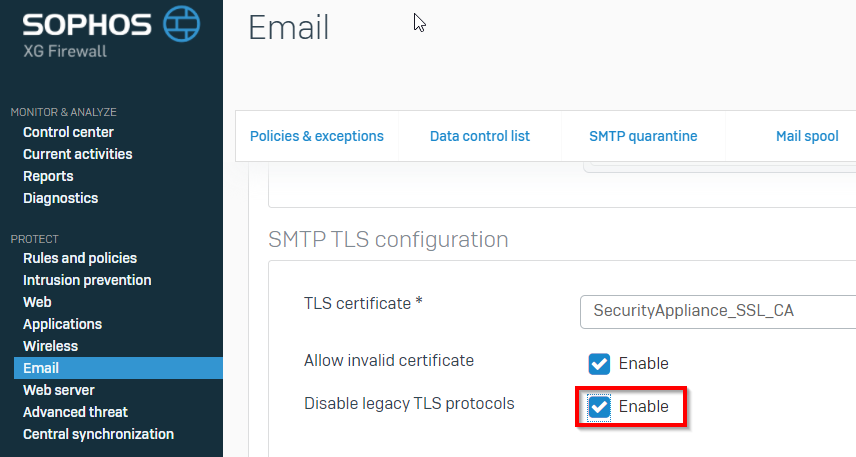
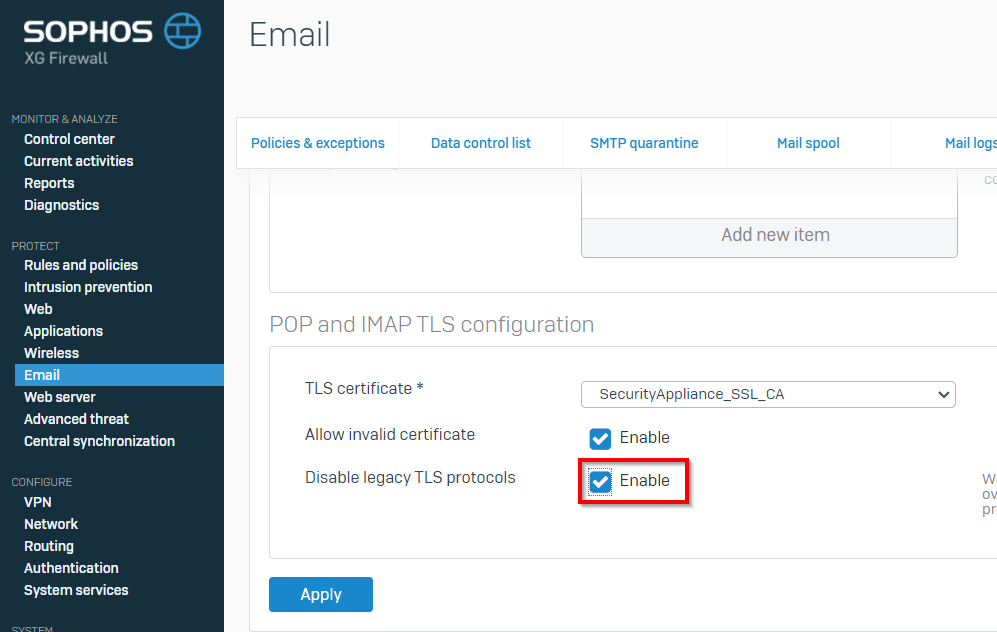
On the same page scroll down to ‘SMTP TLS configuration’ and check the box ‘Disable legacy TLS protocols’, do the same under ‘POP and IMAP TLS configuration’ and don’t forget to click Apply to save the new settings.
From the XG Firewall help:
We recommend that you disable legacy TLS protocols to overcome TLS vulnerabilities. This option will disable protocols earlier than TLS1.1.
4. Enable Advanced threat protection
Go to Protect -> Advanced threat and enable advanced threat protection and change the policy to ‘Log and drop’, then confirm the changes by clicking Apply at the bottom.
From the XG Firewall help:
Advanced threat protection analyzes incoming and outgoing network traffic (for example, DNS requests, HTTP requests, and IP packets) for threats.
Using ATP, you can quickly detect compromised clients in your network and raise an alert or drop the traffic from those clients.
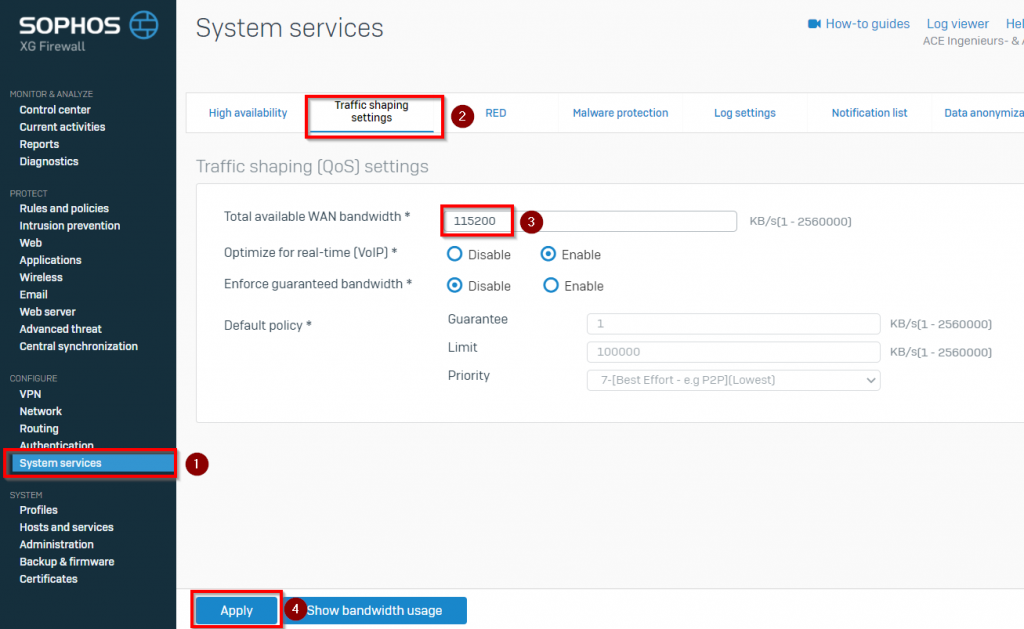
5. Configure your internet bandwidth
Under Configure -> System services choose the tab ‘Traffic shaping settings’ and enter the internet speed that you get from your ISP. Beware the system asks the speed in kilobyte per second rather than the much more common Megabit per second. To convert simply divide the number of Megabit per second by 8 to get the number of Megabyte per second, then multiply by 1024 to get the number of kilobyte per second. The end result is to multiply the number of Mbps by 128.
6. Disable logging of invalid traffic
Now browse to the Log settings tab and deselect ‘Invalid traffic’ under firewall. This is to prevent a lot of log entries with the message: ‘Could not associate packet to any connection’.
It’s not really an issue, but they will be annoying once you need to analyze something in the firewall log. Basically these are dropped packets that came to your firewall. The firewall dropped the packets because a connection that was open before has either been closed or timed-out. After that the firewall doesn’t allow any more packages for the previous connection and drops them.
If you like this post about Sophos XG, you may also like my other posts about Sophos.




Hi.
Awesome guides that are really helpful.
Have you looked at enabling the LCD on the Sophos XG 310 Ref2 and XG 430 Ref1 hardware devices when running XG Home Firewall?
I have both since we changed to Fortigate and want to use either form my home. The LCD would just be a nice extra.
Hi Fred, no I have never looked at the LCD on XG devices with a home install. Maybe someone at the Sophos Community pages could help you with it. Most likely a driver is not inside this installer.
nice post i like it
Hi Lydia, thank you for your message.